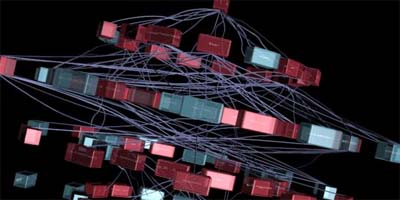
 a 3D animated data visualization showing the structure & execution of the computer virus worm. the boxes are functions of the worm, with the one on the top as the 'main' function where the execution starts. the first ring contains all the functions that 'main' calls, the second all the functions that the ones on the first ones call & so on. all connecting lines represent the calls from one function to the other. red boxes belong to the virus code while the blue ones are API calls library code that do not belong to the malicious code.
a 3D animated data visualization showing the structure & execution of the computer virus worm. the boxes are functions of the worm, with the one on the top as the 'main' function where the execution starts. the first ring contains all the functions that 'main' calls, the second all the functions that the ones on the first ones call & so on. all connecting lines represent the calls from one function to the other. red boxes belong to the virus code while the blue ones are API calls library code that do not belong to the malicious code.
executing computer viruses really seems to be a quite aesthetic activity. [ & & (pdf)]
 Designed and Maintained by
Designed and Maintained by  Time and Date follows Time Zone (Brussels)
Time and Date follows Time Zone (Brussels)