
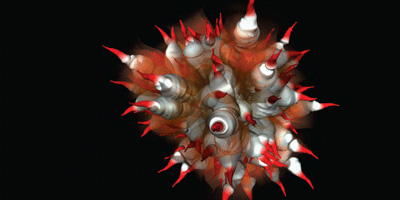
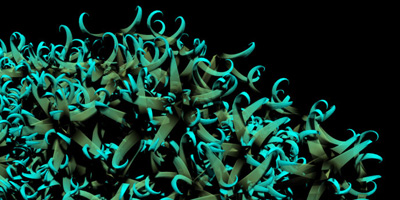
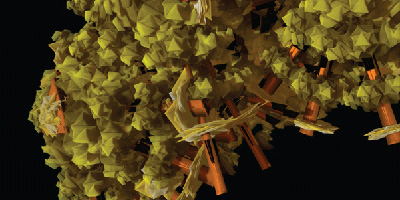
is a series of visualization of worms, viruses, trojans and spyware code. for each piece of disassembled code, API calls, memory addresses and subroutines are tracked and analyzed. their frequency, density and grouping are mapped to the inputs of an algorithm that grows a virtual 3D entity. the entities have been used in campaign to heighten awareness of cyber threats.
[link: & |thnkx jose!]
see also: email spam plants.
 Designed and Maintained by
Designed and Maintained by  Time and Date follows Time Zone (Brussels)
Time and Date follows Time Zone (Brussels)